General Principles
The following apply to all Poolside deployments utilizing Amazon Bedrock for inference, irrespective of deployment support option:- Poolside has no access to customer data models
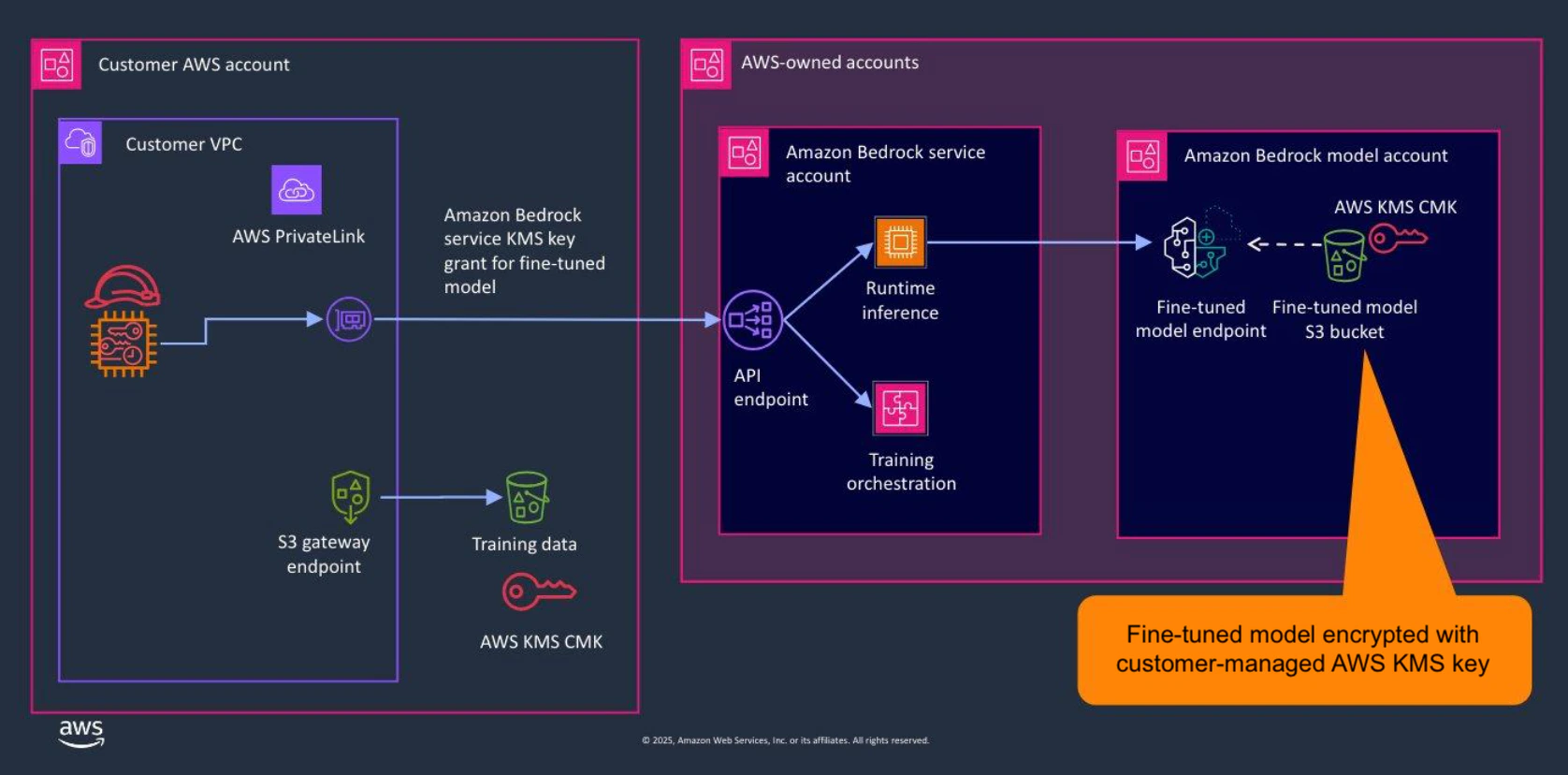
- Prompt and response/completion content is not stored or logged in Amazon Bedrock and is encrypted in-transit with customer-managed AWS KMS keys
- All data transfer between the customer VPC and the Amazon Bedrock endpoint is via AWS PrivateLink (data never traverses the internet)
- IAM policies can be used to restrict access to an authorized subset of models in your Model Deployment Account
Encryption
- All endpoint communication is encrypted in-transit via TLS 1.2 or higher
- Models are encrypted at rest within an Amazon Bedrock Model Deployment Account, which Poolside does not have access to, using customer-managed AWS KMS keys
- Customer data is encrypted at rest with customer-managed AWS KMS keys in the customer VPC
For customers requiring the use of FIPS 140-2 validated cryptographic modules when accessing Amazon Bedrock endpoints, the recommendation is to use a supported FIPS endpoint.
Architecture and Networking
This section outlines how model inference workflows are architected in Amazon Bedrock.Model Inference
Cross-Region Deployments
Cross-region deployments (where the customer VPC is in a different AWS Region from the Amazon Bedrock endpoint) may be required if an Amazon Bedrock endpoint with support for Poolside is not available in the customer’s preferred VPC region. This is enabled by Inter-Region VPC peering between the ‘local’ customer VPC and a ‘transit’ customer VPC in the Amazon Bedrock endpoint region.- VPC peering connections use private IP addresses only, and do not involve internet gateways, NAT gateways, or VPN connections
- Route tables in the ‘local’ customer VPC direct traffic to the Amazon Bedrock endpoint via the ‘transit’ customer VPC
- AWS PrivateLink establishes private connectivity between the ‘transit’ customer VPC and the Amazon Bedrock endpoint
Customer data remains encrypted at rest in the ‘local’ customer VPC region, and is never stored at rest in the Amazon Bedrock endpoint region.
Audit Trails and Logging
- AWS CloudWatch is supported (in addition to Poolside-provided telemetry), providing metrics on model invocation, latency, client-/server-side errors, throttling, etc.
- Audit trails are available in AWS CloudTrail (in addition to Poolside-provided logging), i.e., all API calls made to Amazon Bedrock endpoints, capturing details such as caller identity, time of request and request parameters.
- Event alerts are available in Amazon EventBridge, enabling the creation of rules that trigger actions in response to an event.